Understanding VLAN
Hello everyone! Today, i will give you an brief overview about Virtual Local Area Networks (VLANs). VLANs are a fundamental concept in modern networking that offer numerous benefits, from enhanced network segmentation to improved security and efficiency. So, let’s explore what VLANs are and why they matter!
Router on Stick Configration Example

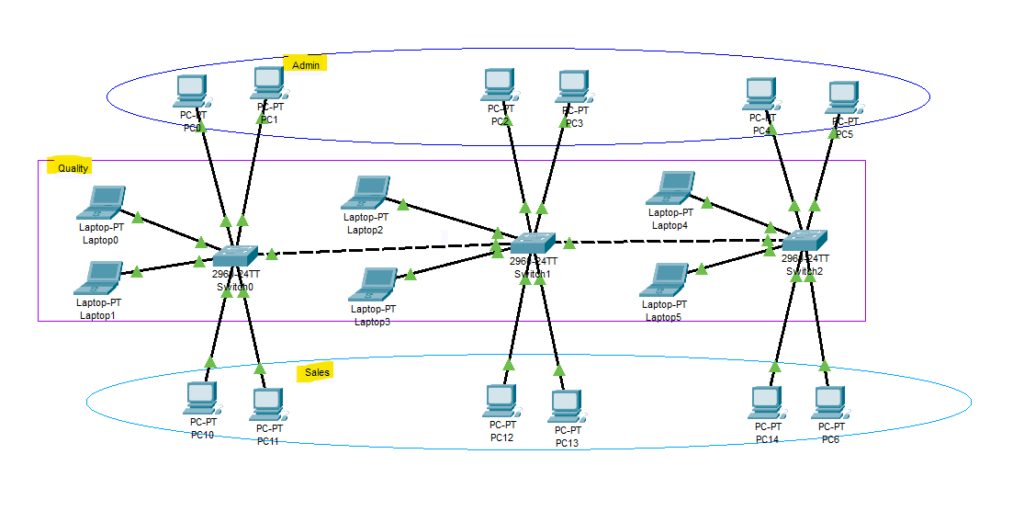
Basic Vlan Configration Example
What is a VLAN?
A VLAN, or Virtual Local Area Network, is a logical segmentation of a physical network into multiple smaller, isolated networks. Unlike traditional physical LANs, where devices are grouped based on their physical location, VLANs allow you to group devices logically based on factors like department, function, or security requirements, regardless of their physical placement.
VLAN Configuration types
- Basic Configuration VLAN
Router On Stick VLAN
Svi Multilayer Switch VLAN
- Inter VLAN Routing
Key Benefits of VLANs
Enhanced Network Segmentation
VLANs enable the creation of distinct broadcast domains, reducing network traffic and collisions. This segmentation enhances performance by isolating traffic and ensuring that devices within a VLAN can communicate directly with each other without interfering with devices on other VLANs.
Improved Security
By dividing the network into separate VLANs, you can isolate sensitive data and critical resources from the rest of the network. This isolation provides an additional layer of security, limiting unauthorized access and minimizing the potential impact of security breaches.
Simplified Network Management:
VLANs make network administration more efficient. Instead of managing individual physical LANs, IT administrators can organize devices and users into VLANs based on their roles or needs. This simplifies network management tasks, such as configuring access controls, implementing Quality of Service (QoS), and troubleshooting network issues.
Flexibility and Scalability
VLANs allow for a more flexible and scalable network infrastructure. As your organization grows or changes, you can easily adjust VLAN memberships to accommodate new devices or users without physically rewiring the network.
Types of VLANs
Port-Based VLANs
In port-based VLANs, devices are assigned to VLANs based on the physical port to which they are connected on a switch. Devices connected to the same port belong to the same VLAN.
Tagged VLANs
Tagged VLANs are used in situations where multiple VLANs need to traverse a single physical link, such as when connecting multiple switches together. Tags are added to the Ethernet frames, indicating which VLAN the frame belongs to.
MAC-Based VLANs
MAC-Based VLANs assign devices to VLANs based on their Media Access Control (MAC) addresses. This approach is useful when devices move across different physical ports but need to remain in the same VLAN.
Protocol-Based VLANs
Protocol-Based VLANs classify traffic based on the Layer 3 protocol information in the packet headers. This is particularly helpful in separating voice, video, and data traffic for improved QoS.
In summary, Virtual Local Area Networks (VLANs) are an essential tool for modern network administrators seeking to optimize network performance, enhance security, and streamline network management. By logically segmenting the network and isolating traffic, VLANs provide a robust and scalable solution for meeting the demands of complex IT environments.
So, if you want to create a more efficient, secure, and manageable network, consider implementing VLANs as part of your network architecture. Happy networking! 😊🔌🌐
FAQ
| Question | Answer |
|---|---|
| What is a VLAN? | A VLAN, or Virtual Local Area Network, is a network segmentation technique that enables the creation of multiple logical networks within a physical network. VLANs help isolate broadcast domains, improve network performance, and enhance security. |
| Why are VLANs used? | VLANs are used to organize network traffic, improve performance, and enhance security. By dividing a network into VLANs, administrators can control broadcast domains, manage traffic efficiently, and isolate devices logically. |
| How do VLANs work? | VLANs work by assigning specific ports or devices to virtual networks. This grouping allows for the segregation of traffic, making it functionally separate from other VLANs, even though they may share the same physical infrastructure. |
| What is VLAN tagging? | VLAN tagging involves adding a unique identifier (VLAN tag) to Ethernet frames. This tag helps network devices identify which VLAN a particular frame belongs to, allowing for proper handling and routing within the VLAN. |
| How are VLANs configured? | VLANs can be configured on network switches through the switch’s management interface. Administrators assign VLAN membership to specific switch ports, and devices connected to those ports are part of the corresponding VLAN. |
| What is the purpose of VLAN trunking? | VLAN trunking enables the transportation of multiple VLANs over a single network link (trunk). This is commonly used between switches to carry traffic for different VLANs, ensuring efficient communication across the network. |
| Can VLANs span multiple switches? | Yes, VLANs can span multiple switches through VLAN trunking. This allows for consistent VLAN configurations and communication between devices on different switches while maintaining logical separation. |
| How do VLANs enhance security? | VLANs enhance security by isolating broadcast domains and logically separating network traffic. This segmentation restricts unauthorized access to sensitive information and mitigates the impact of network security incidents. |
| What is the impact of VLANs on network performance? | VLANs can improve network performance by reducing broadcast traffic and optimizing the use of network resources. By segregating traffic, VLANs minimize unnecessary data transmission to devices that don’t require it. |
| Can VLANs be used for VoIP implementations? | Yes, VLANs are commonly used for Voice over Internet Protocol (VoIP) implementations. They allow for prioritization of voice traffic, ensuring quality communication by separating voice data from other types of network traffic. |
| How does VLAN implementation affect network management? | VLAN implementation streamlines network management by providing a structured approach to organizing devices and controlling traffic. It simplifies troubleshooting, facilitates resource allocation, and enhances overall network efficiency. |
Read More – Unlocking Cybersecurity Insights 2024: Power of Virus Total

